Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve received an urgent email seemingly from your boss. But something felt off. Welcome to the world of deepfakes. This is a rapidly evolving technology that uses artificial intelligence (AI). It […]
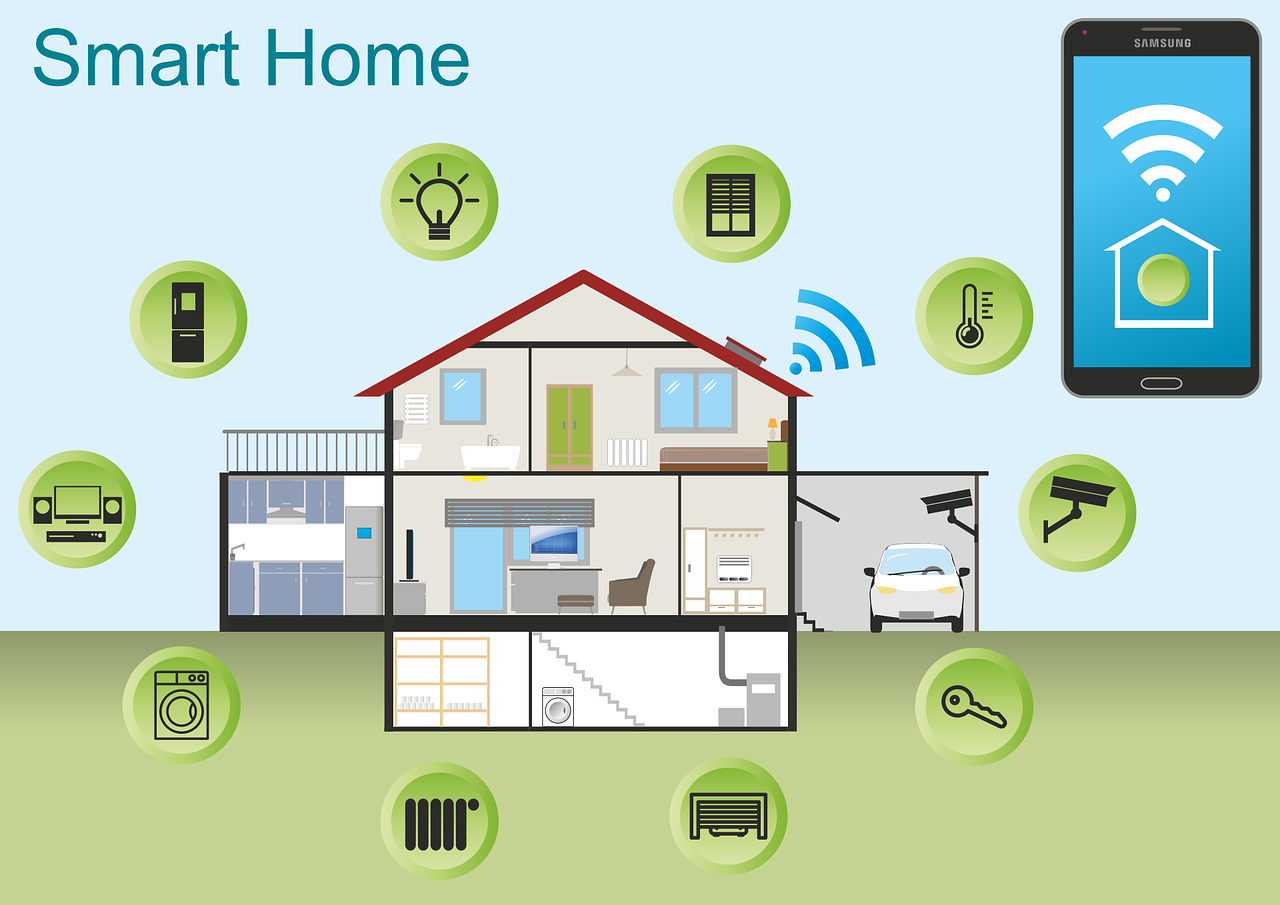
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators and voice-activated lights. But even the most advanced technology can have analog […]
Relentless digital innovation has defined the last few years. The symbiotic relationship between AI and cybersecurity has become pivotal especially when it comes to safeguarding sensitive information and digital assets. As cyber threats evolve in complexity, AI has emerged as a formidable ally. It empowers organizations with advanced tools and techniques. Helping them to stay […]
Browser extensions have become as common as mobile apps. People tend to download many and use few. There are over 176,000 browser extensions available on Google Chrome alone. These extensions offer users extra functionalities and customization options. While browser extensions enhance the browsing experience, they also pose a danger which can mean significant risks to […]
In the digital age, data is the lifeblood of businesses. It fuels operations, decision-making, and customer interactions. But there is a dark underbelly of this data-centric landscape. It’s the persistent threat of data breaches. The repercussions of a data breach extend far beyond the immediate aftermath. They often haunt businesses for years. Only 51% of […]
The integration of smart home devices has become synonymous with modern living. They offer convenience, efficiency, and connectivity at our fingertips. But a recent study has raised concerns about the darker side of these smart gadgets. It suggests that our beloved smart home devices may be spying on us. It’s natural these days to invite […]
Cybersecurity has become paramount for businesses across the globe. As technology advances, so do the threats. Recognizing this, the U.S. Securities and Exchange Commission (SEC) has introduced new rules. They revolve around cybersecurity. These new requirements are set to significantly impact businesses. These rules are a response to the growing sophistication of cyber threats. As […]
The global cost of a data breach last year was USD $4.45 million. This is an increase of 15% over three years. As we step into 2024, it’s crucial to be aware of emerging technology threats. Ones that could potentially disrupt and harm your business. Technology is evolving at a rapid pace. It’s bringing new […]
Breached or stolen passwords are the bane of any organization’s cybersecurity. Passwords cause over 80% of data breaches. Hackers get in using stolen, weak, or reused (and easily breached) passwords. But passwords are a part of life. Technologies like biometrics or passkeys haven’t yet replaced them. We use them for websites, apps, and more. So, […]